Operation Popey is purportedly a high-level covert program that combined psychological operations, advanced monitoring, and experimental formats that crossed the lines of science, warfare, and manipulation.
Although it was not official, the circumstantial evidence and scope of the details are enough to suggest that there was something about this operation that had real-world implications and likely was a harbinger to future strategic innovations.
The term “Popey” is a codename and likely refers to someone who is depicted as being strong and unpredictable.
Whether this is symbolic or arbitrary is up for debate, there is no debate that Operation Popey was not a normal operation.
Contents
- 1 Historical Context and Background
- 2 Operation Popeye – Weather Warfare in Vietnam
- 3 Objectives of Operation Popey
- 4 Planning, Preparation, and Logistics
- 5 Detailed Timeline of Events
- 6 Key Agencies and Individuals Involved
- 7 Operation Popey Results and Impact
- 8 Public Awareness and Media Coverage
- 9 Ethical Concerns and Controversies
- 10 Long-Term Legacy of Operation Popey
- 11 Conclusion
Historical Context and Background
In order to understand Operation Popey we need to consider the global context of its theorized time period – roughly the late 1990’s – mid 2000’s.
The Post Cold War Era
After the Cold War, military strategy transitioned to more asymmetric warfare, including:
- Cyber warfare
- Espionage
- Intelligence led operations
- PsyOps
As the balance of power evolved nationally and internationally, nations pursued ways of influencing others that were less direct.
This may have been the environment where Operation Popey developed—this blend of psychological warfare and new technologies.
You may like to read:
Climate of Fear and Control
In the early 2000’s fear created a climate dominated by worry about terrorism, rogue states, and mass surveillance.
The world’s governments built up they covert programs globally.
In the midst of this craze, many projects were tested that sounded like science fiction but were very real.
In addition to geo-engineering and other forms of weather manipulation, projects like mass data harvesting and neural influence were tested.
Operation Popeye – Weather Warfare in Vietnam
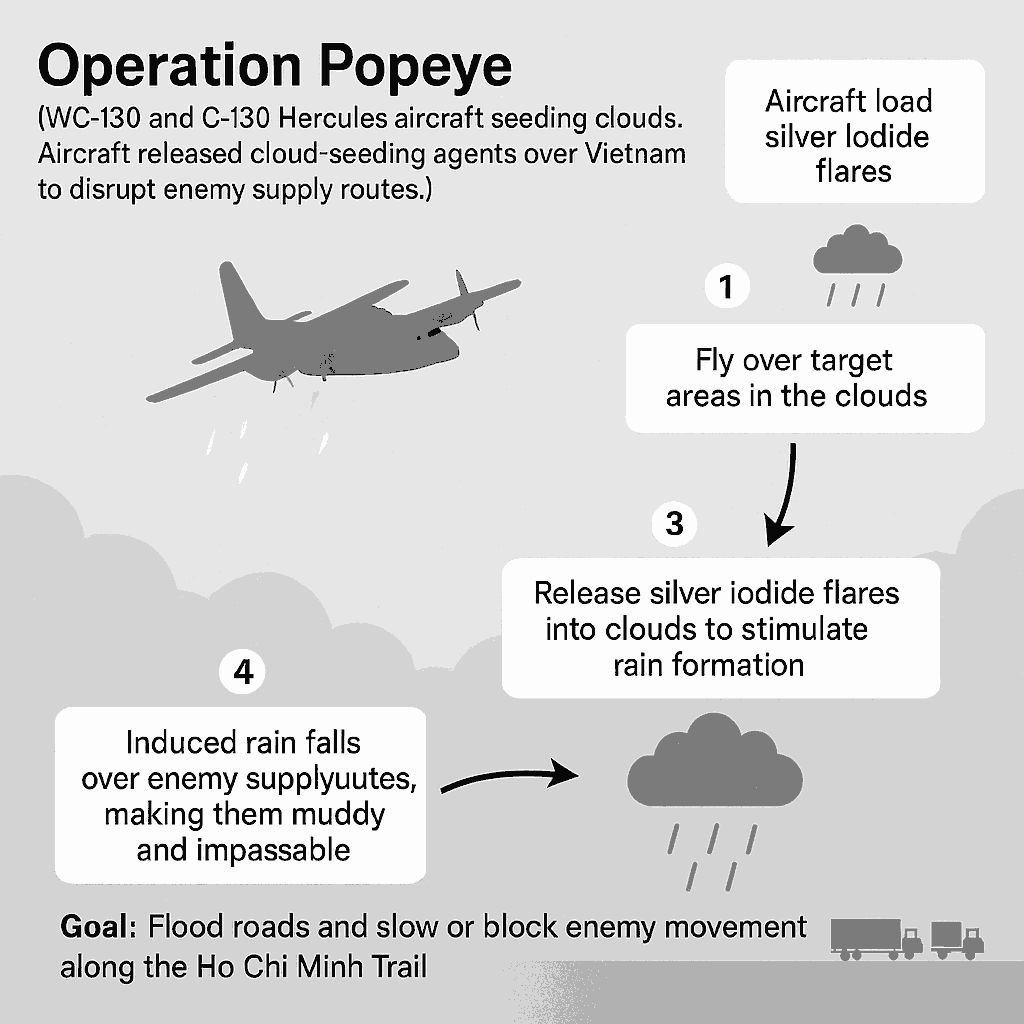
In the image above you can see how U.S. aircraft utilized cloud seeding in Vietnam War.
- The aircraft were loaded with silver iodide flares,
- Flew over and into the clouds they were trying to affect
- Released the flares to create the rainfall.
- The large volume of rainfall then caused flooding and damage to the enemy supply routes of the Ho Chi Minh Trail, which delayed the enemy from traveling to their intended destination.
Objectives of Operation Popey
The suspected objectives of Operation Popey, while never officially confirmed, may have been broad and maybe experimental in nature.
Intelligence analysts believe there was some level of purposeful within the suspected objectives of Operation Popey, for example:
Psychological Manipulation
There may have been an key objective of assessing and manipulating public perception.
Methods may have included disinformation campaigns, mass behavioral experimentation, and engaging public perception through various influences such as media and their environmental situation.
Atmospheric or Environmental experimentation
Some researchers suggest Operation Popey was linked to attempts at weather manipulation, akin to Project Popeye during the Vietnam War — an actual weather warfare project aimed at extending monsoon seasons.
If connected, Operation Popey may have tested:
- Cloud Seeding
- Geoengineering
- Weather modification and disruption using electromagnetic forces
Data Collection and Monitoring
Continuing the capability to monitor populations in a mostly covert way on the digital or real world.
It is unlikely AI and algorithms are being used, and it is also unlikely they are in the first and early stages of testing.
Testing to Access Through Backdoor Communication
In contested areas or politically queried regions, it is imperative that secure covert communication is undertaken.
Operation Popey potentially has experimented with less visible data emissions.
Planning, Preparation, and Logistics
Running a clandestine operation such as Operation Popey would require careful planning, exact logistics, and absolute secrecy. Planning would likely require:
Team Selection
- Elite operatives from intelligence services
- Imminent scientists for psychology, meteorology, and data scientists
- Engineers who work on aerospace and satellite systems
Budget and Resources
Classified operations may be funded by “black budget” resources — in other words, off the record allocations of funding that would not appear in the public accounts.
This fact allows for vast resources to be allocated without checks.
Location Finding
Operation Popey may have operated in:
- Remote areas where population density is limited.
- Disputed/unstable political areas.
- Urban areas as part of the psychological exploratory studies.
Detailed Timeline of Events
While no dates are certain, here is a timeline based on the analysis of current projects.
1990s – Forming and Planning
- Strategic needs developed
- Preliminary technology tested in laboratory environments
- Collaboration of coalition force intelligence agencies
2001–2003 – Prototyping and ancillary field simulations
- Testing small scale experiments
- Observation of behavior and reactions of the public
- Data analysis and revision of mission
2004–2006 – Full operational deployment
- Peak operational activity
- Use of covert technology and covert operations
- Unofficial reports of odd environmental aspects in some areas
2007 onward – Mission shutdown, evolution
- Program is either decommissioned or assumed an alternate branding.
- Research findings were integrated into larger strategic programs.
Key Agencies and Individuals Involved
Intelligence Agencies (Suspected):
- CIA (Central Intelligence Agency) – U.S. psychological operations and global intelligence
- NSA (National Security Agency) – Communication interception and cybersecurity
- DARPA – Advanced tech and AI testing
- MI6 and GCHQ (UK) – International coordination of surveillance
Contractors and Private Entities
Often it is easier to outsource operations to private companies for:
- Plausible deniability,
- Advanced R&D capability, and
- Elimination of any red tape.
Additionally, the companies in aerospace, cloud computing, and and behavioral sciences could have played a silent role.
Operation Popey Results and Impact
While still unofficial, the effects of Operation Popey seem to have affected a few areas:
➤ Psychological Warfare Capabilities
The operation seems to have increased awareness of mass influence, and could possibly influence the next generation of information warfare doctrine.
➤ Military doctrine change
The operation likely influenced a change in military thinking about using non-lethal influence tactics in lieu of combat, providing historical reference to thinking other than combat.
➤ Technological advantage shift
Some of the technologies we currently use for surveillance and remote influence may be based on the experiments completed during this mission.
Public Awareness and Media Coverage
For several years, people have wrongly believed that the operational environment and ramifications of Operation Popey have been, and continue to be, sequestered away in secrecy.
However, a completely new phase passed when whistleblowers, freelance journalists, and digital pattern analysis began utilizing references under Popey.
Documentary Snippets and Leaks
There are a few independent documentaries on the internet hammering on “unnamed” operations that appear to describe the characteristics of Popey.
In 2014, documents were leaked from a very well-publicized global leaks platform and provided some operations that described whether-tracing operations assigning codename Popey.
Online Community Engagement
There have been many online conversations between conspiracy theorists and open-source investigators – actively working for years to leap the mission and logic of the operation by a collective run on their favorite forums and podcasts.
Even though the community has put so much energy attempting to push content in this space, the coverage in recognizable news patterns has diminished.
Perhaps this is a result of the ongoing, active classification and/or potential validation.
Ethical Concerns and Controversies
Popey style activities raise a large number of ethical implications particularly if all operates via collective channeling or collective experimentation without consent.
Some obvious challenges are:
- Lack of transparency – Regardless of the proxies and constraints of democratic countries oversight, accountability takes place in secret.
- Environmental liability – If the activities have any manipulative aspect of weather, and have unintended consequences, it could create significant, if not dangerous, risks.
- Sovereignty – If the testing occurs in countries other than Canada, and this is what the tests conclude, then this may be a breach of international law.
- Human Rights – The manner in which this exploration is conducted is also unethical, especially where you are using civilian populations as subject matters in psychological tests without their consent.
There is an important point to note where the issue of ethical dilemma is concerned, advocacy, watchdog organizations and others when gathered as proof of declassification and transparency accountability.
Long-Term Legacy of Operation Popey
The implications of Operation Popey may be insidious, but they are vast. It may have influenced:
- Contemporary surveillance infrastructure
- PsyOps training regimes
- AI-behavioral modeling systems
- Civil-military technology cooperatives
In retrospect, Operation Popey may have been less about protecting or securing an objective, and instead a prototype for a novel form of warfare — invisible, psychological, and technologically mediated.
Conclusion
Operation Popey occupies a gray area in intelligence operations history — unverified, but persistently dubbed “influential.”
Fragments derived from leaked material, independent investigations, and world speculation illustrate a mission that was ambitious and covert.
As either a psychological exploration, weather manipulation experiment, or reconnaissance trial,
Operation Popey contributed to a larger change in warfare based not on bombs, but in influence, data, and perception.
Understanding portions of Operation Popey allows us to challenge the unseen forces influencing public thought, environmental circumstances, and world stories as we enter the 21st century.
